BlueCap
- Leverage Bluecap Secure OS
- Device Integrity Attestation
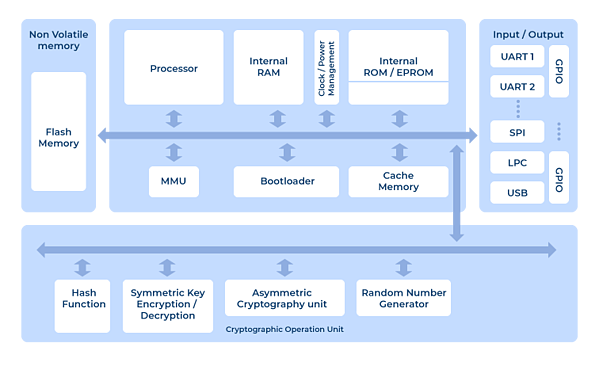
- Hardware Asymmetric Crypto-processor
- Internal EEPROM Storage for Keys
- Secure Hardware and Firmware Design Layout
- FIPS-140-2 Certified Including RNG, HMAC, AES, SHA, and RSA Engines
Request a Demo
IoT devices should be tamper-resistant and impregnable to malicious software. BlueCap offers state-of-the-art hardware based security and protection against a wide array of attack vectors even with physical access to your IoT devices.
HSMs (hardware security modules) are widely adopted by industries that require high levels of security such as banking and IoT, the powerful and flexible crypto-processor offered by BlueCap HSM can create, manage and use cryptographic keys, as well as store confidential data. BlueCap is intimately tied into into different operating system stages including boot and runs, which means it is far more powerful and useful than any software based security solution.
IoT Protection with BlueCap
The rise of IoT enabled organizations to more easily expand their businesses and services around the world, that raises the need for encryption, decryption and strong authentication between identities and applications. For these purposes, organizations deploy HSM (hardware security modules) for the protection of clients and business transactions.
Tier One Security
The usage of HSMs provides cryptographic throughput and results in a more secure and efficient architecture for different solution. The HSM becomes an invaluable component of the security solution, which not only minimizes business risks but also achieves state-of-the-art performance in cryptographic operations.
A security control is only effective if applied with the correct and proper measurements and understanding. Similarly, an HSM provides “foolproof” security for key management if the solution architecture design, application level implementation, security analysis, user education and security policy of the product are given proper research and considerations.